If your team connects to office computers from home, your bookkeeper dials in from a client site, or anyone on your network opens Remote Desktop files emailed from third parties, Microsoft’s April 2026 security update changes how those connections look — and it’s changing for the better. Starting with this month’s Patch Tuesday (April 14, 2026), Windows shows a prominent warning every time someone opens an .rdp file, with the exact wording of the warning dependent on whether that file can be trusted.
Here’s what you’ll see, what it means, and what we recommend.
The new warning dialogs, in pictures
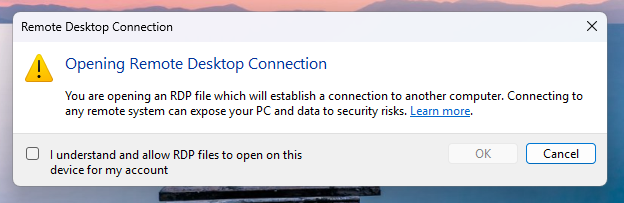
The first time any user on an updated Windows machine opens an RDP file, they’ll see an educational prompt explaining what RDP is and why it’s a phishing target. This screen appears once per user account, so the first time someone on your team opens a legitimate RDP file after the April update lands, don’t be alarmed.
From that point forward, every .rdp file triggers a connection-security dialog, and the dialog comes in two flavors.
🟧 Unsigned RDP files — “Caution: Unknown remote connection”
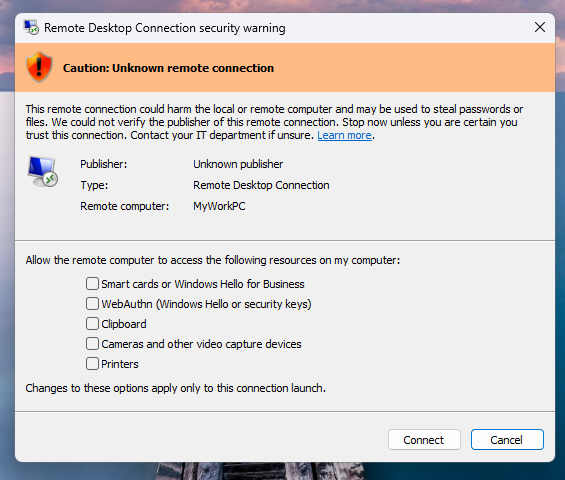
If someone emails your team an RDP file and Windows shows this orange banner with “Unknown publisher”, treat it as a phishing attempt until proven otherwise. An attacker could have spun up an RDP server, crafted an .rdp file that silently redirects your local drives or clipboard to their server, and mailed it in a message that looks like a routine IT request. That’s not theoretical — Microsoft cites active phishing campaigns as the reason this dialog now exists (the fix is tracked as CVE-2026-26151, reported by the UK’s National Cyber Security Centre).
✅ Signed RDP files — “Verify the publisher of this remote connection”
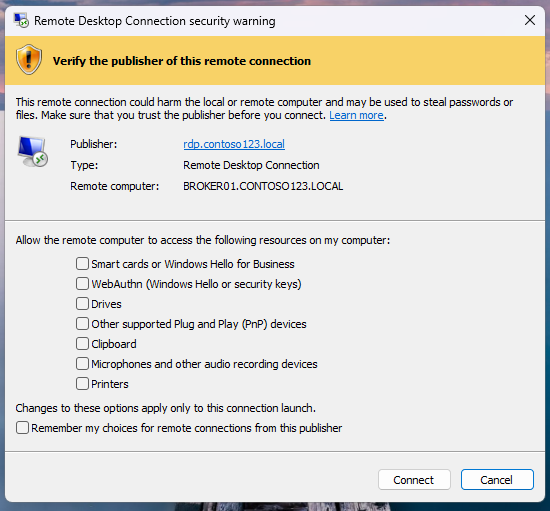
When your IT provider or an approved vendor distributes RDP files, the file should be digitally signed — and this dialog will show their name. Read the publisher name carefully. A digital signature proves the file wasn’t tampered with in transit, but it doesn’t prove the signer is legitimate; attackers have been known to register names that closely resemble real organizations.
Everything is off by default now
The bigger change most users won’t notice until it matters: every local device redirection — drives, clipboard, microphone, camera, smart cards, printers — is now off by default when you open an RDP file. You have to explicitly check the box for each resource you want to share.
This is a big deal because most RDP phishing attacks depend on those redirections being enabled. If you connect with everything off, an attacker on the other end sees… just a screen. No access to your files, no clipboard to read your passwords out of, no microphone to eavesdrop with.
The practical takeaway: only enable the redirections you actually need. If you’re connecting to a work PC to run an application, you probably don’t need clipboard sharing — and you definitely don’t need drive sharing.
WebAuthn and passkey redirection warnings
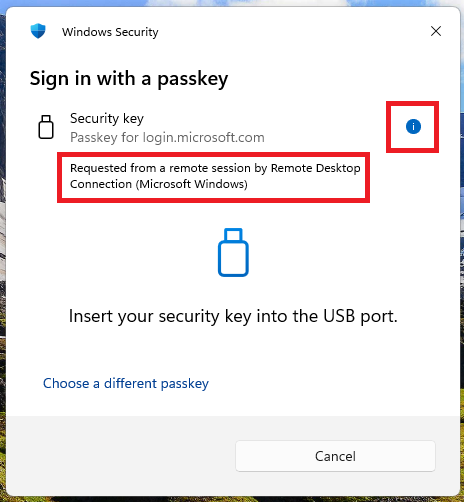
If you use Windows Hello, a FIDO2 security key, or passkeys, there’s one more change to know about: when a remote session asks you to authenticate, Windows now labels the prompt as coming from a remote session. That’s your cue to stop and think. If you weren’t just asked to sign in by something on the remote side, an attacker might be trying to redirect your authentication challenge through a session you’re already in.
What else April 2026 Patch Tuesday fixed
The .rdp dialog gets the headlines, but April was a big month overall — 163 CVEs patched, 8 rated Critical. Besides the RDP work already mentioned, these RDP-adjacent items stood out:
- CVE-2026-26159 — Remote Desktop Licensing Service elevation of privilege. If you still run RDS Licensing on Windows Server, patch it.
- CVE-2026-32157 — Remote Desktop Client remote code execution. An attacker who tricks a user into clicking an
rdp:link can run code on the client. The new dialog helps, but the underlying flaw is patched by the update. - CVE-2026-32201 — the headline Critical of the month, a Secure Boot bypass that’s been publicly disclosed.
Your checklist
- Make sure every Windows endpoint is patched — especially anything you remote into or remote from.
- Don’t open unexpected RDP files, even from people you know. Confirm via phone or a fresh email thread.
- If the orange “Unknown publisher” banner appears on a file you got from your IT provider, pause and ask — your provider should be signing RDP files they distribute.
- Keep local redirections off unless you genuinely need them. Drives and clipboard are the two most-abused settings.
- Treat any “Requested from a remote session” authentication prompt you didn’t expect as a phishing attempt — don’t approve it.
If you’re a HiveTech managed client
Your devices are already on our patch cadence, so the April update is either rolling out or already applied. If you notice the new dialog on a connection we manage for you and want us to sign our RDP files so the green-checkmark experience appears instead, reply to this post or email support and we’ll add code-signing to our deployment pipeline.
If you’re running RDP-based remote access outside our managed environment and want us to review it — happy to help. The new Windows dialogs close a real attack vector, but the best time to audit who’s connecting to your stuff is before an attacker does it first.
Further reading: Microsoft’s official guidance on the new RDP security warnings.
